Smart Barcode Scanning System
Barcode Scanner App for iOS and Android
The barcode scanner app can be installed on smartphones, tablets or rugged mobile computers to scan barcodes, collect additional data and sync all the data to the cloud or your database.
Cloud-based Management Portal
The cloud-based system serves as a centralized hub for managing app users, setting up data collection processes for barcode scanners, and seamlessly handling the storage, organization, export, and integration of scan data with other business systems.
No credit card required to create a test account.

Popular Barcode Scanner App Configurations

Ticket Scanning App
Our mobile barcode scanning app integrates seamlessly with our cloud-based ticket validation infrastructure, ensuring smooth handling of events of any scale. From intimate training sessions with twenty participants to massive concerts attracting crowds of tens of thousands, our app adapts effortlessly, whether deployed on a single device or across a fleet of hundreds, facilitating efficient ticket redemption processes.
Ticket validation, works offline if required
Duplicate ticket checking and controlled re-entry
Customizable ticket validation criteria
Attendance Tracking App
Now, schools, associations, and businesses can harness the power of smartphones and tablets for access control and attendance recording. With our barcode scanning app tailored for event attendance tracking, IDs and passes belonging to students, members, guests, and employees can be swiftly scanned, ensuring efficient management and accurate record-keeping.
Check-in and check out attendees
. Control attendee access at remote locations
. Control capacity and track duration

Logistics Scanning App
Manufacturers and shipping fulfillment centers rely on CodeREADr for seamless processing of numerous work orders daily. Tailored for efficiency, our app is customizable to swiftly scan and validate product codes against corresponding work orders, ensuring smooth operations.
Pick, Pack, Ship, Deliver, and Receive
Track warehouse locations and work-in-process
Track asset status and locations globally

Inventory Audit App
Easily monitor inventory status in real-time, regardless of location or time. Enhance accuracy by leveraging precise barcode scanning capabilities and an intuitive user interface designed for capturing inventory quantities and related data effortlessly. Enable staff members to log in and conduct scans seamlessly from any location.
Conduct inventory audits onsite or remotely
Build databases and track errors
Audit inventory with or without connectivity
Security & Maintenance Tracking App
Effortlessly create your property inspection application for both iOS and Android devices with just a few simple steps. Enable your app users to efficiently gather the required on-premise data for client reporting and maintaining compliance with regulations. Enhance your inspection processes by leveraging our intuitive platform tailored for seamless data capture and management.
Remotely track security teams
Document incidents with asset, location and photos
Offer proof of performance to stakeholders
Cloud-based Management Portal
Manage app users, configure data collection workflows for your barcode scanning devices, and store, organize, export and integrate your barcode scan data with your other business systems.
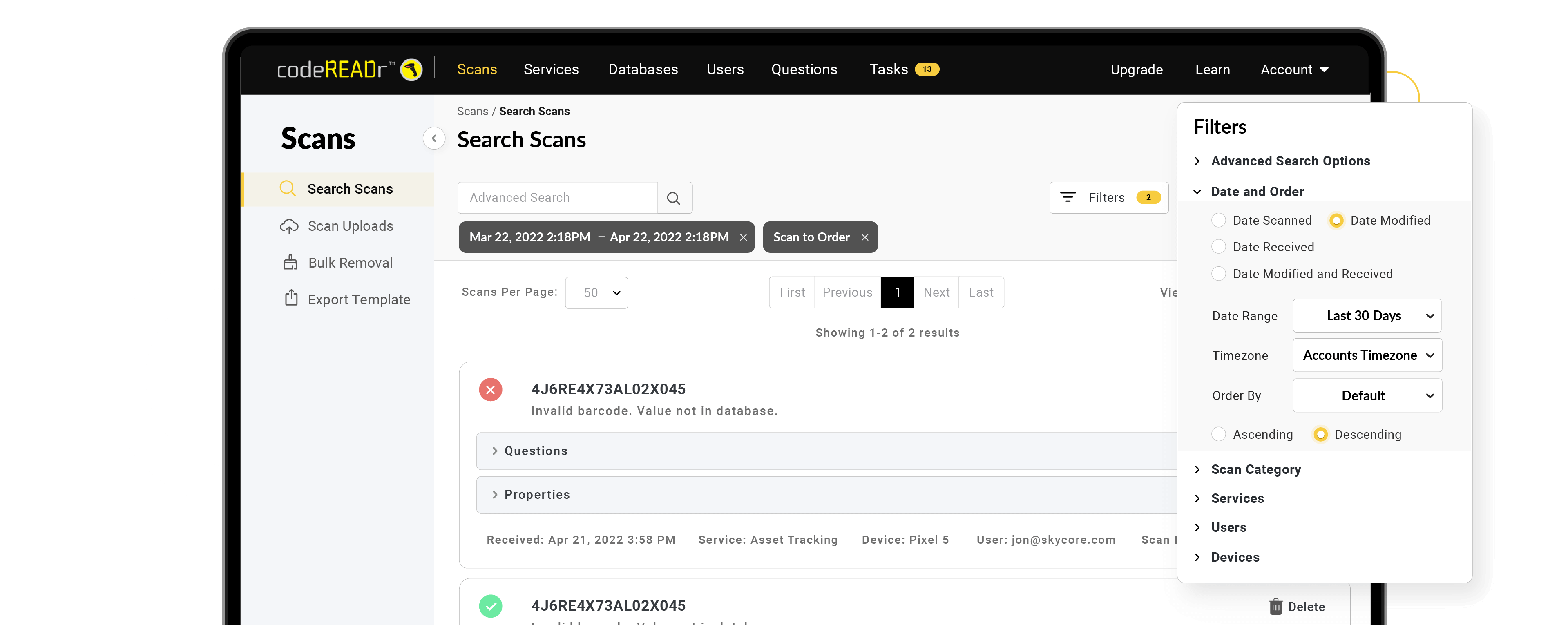
Service Workflow Management
Setup custom workflows for your barcode scanning and data collection services.
Validation Database Management
Import, export, integrate and edit your validation database in the cloud.
Form and Question Management
Prompt app-users to collect data and customize the validation of that data.
App User Management
Manage user permissions, devices, service workflows, databases, scan history and reports.
API for Integration
The API gives you full control of scanning devices, users, and data.
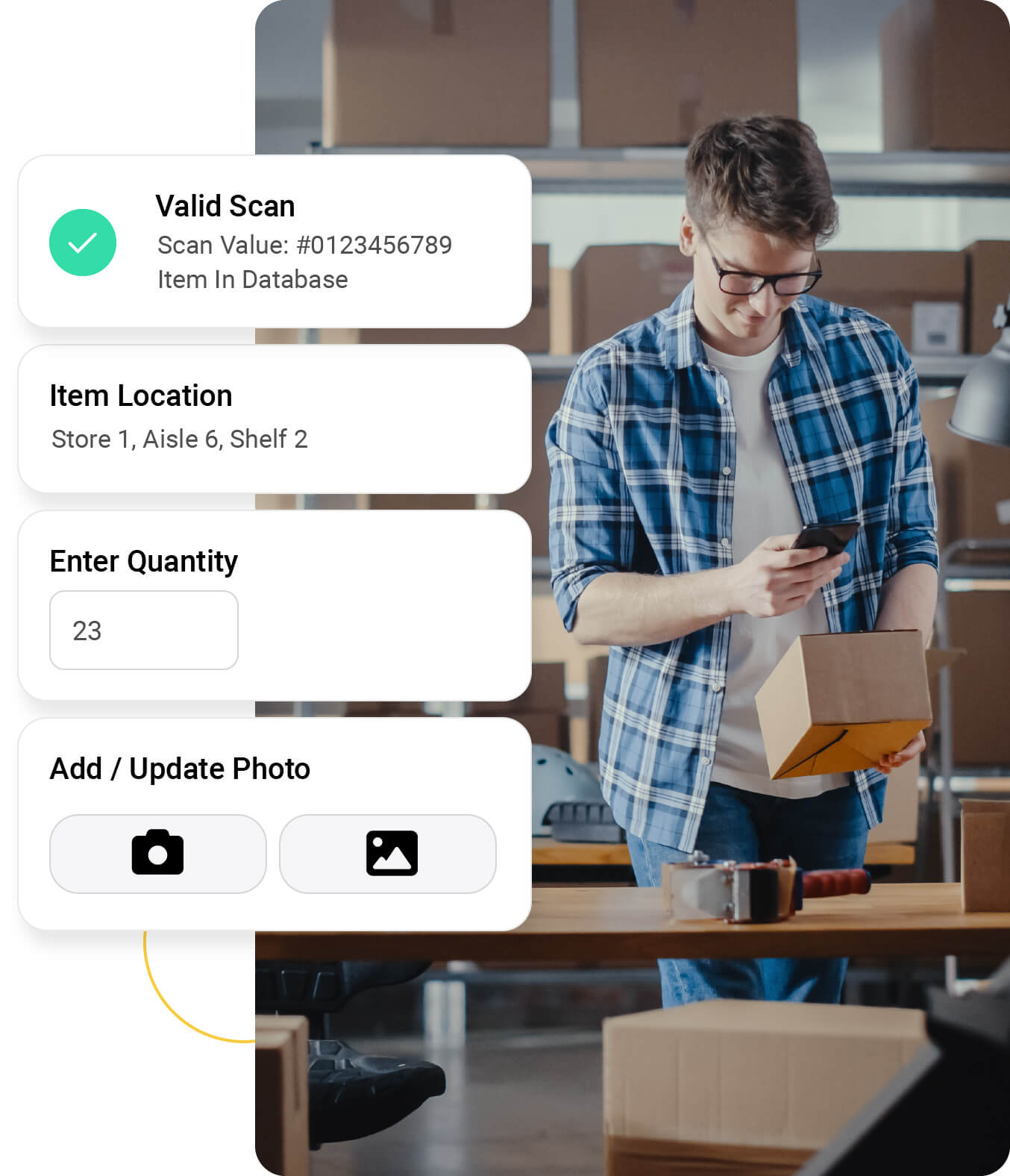
Scan barcodes, collect data, and seamlessly sync to the cloud or your database.
Quickly and accurately scan barcodes utilizing your device’s camera, imager, or Bluetooth scanning accessory. Prompt for additional info using a variety of formats including multiple-choice, drop-down, voice-to-text, or customizable fields.
Scan technologies include scanning 200 barcodes in seconds, augmented reality, alter-scan, alter-response, scan filtering, and custom validations.
Works Offline
If online connectivity is unstable, scans are saved on the app and synced every 2-seconds to the cloud.
Validate Scans in Real-Time
Validate barcode scans against a database stored in the cloud or a database stored on your device.
Supports a Wide Variety of Device Types
Use the app with smartphones, tablets, scan sleds, and Android based mobile computers. Scan barcodes with the built-in camera, a hardware imager or a Bluetooth barcode scanner.

iOS and Android OS
Smartphones

iOS and Android OS
Tablets

iOS and Android OS
Scan Sleds

Android OS
Rugged Mobile Computers
Android OS
Chromebooks

iOS and Android OS
Bluetooth Scanners
Our Customers Include
TRUSTED BY