December 16, 2018 • 10 min read
Enhanced Security in Event Management: QR Code Scanning for Lead Retrieval

CATEGORIES
SOCIAL SHARE
Decrypting Encrypted QR Code IDs and Badges with Advanced Barcode Scanner Apps
In today’s digital age, securing Personally Identifiable Information (PII) has become paramount, especially in environments like trade shows and expositions. With the introduction of GDPR, there’s a heightened emphasis on the secure handling of PII, which now extends to both digital and printed materials. This blog post explores how encrypted QR codes, barcodes (including PDF-417 and DataMatrix formats), and NFC tags are set to become the norm for encoding sensitive data on event badges and IDs.
Focus on Trade Show Badges for Expositions
Trade shows have significantly adapted in response to GDPR, affecting the generation and printing of attendee badges. These badges often contain QR codes or barcodes that encode contact details such as name, company, address, email, and phone number, primarily used for lead retrieval purposes. However, the traditional method of embedding readable QR codes poses a privacy risk, as anyone with a generic QR code scanner can access an attendee’s personal details.
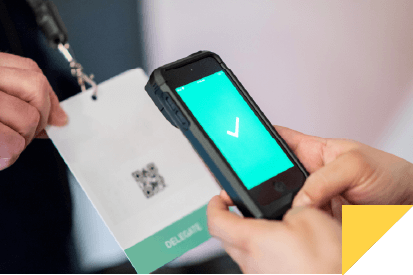
Secure Lead Retrieval Through Barcode Scanning
The traditional lead retrieval process involves scanning a badge’s QR code to store attendee contact information for post-event follow-up. While this method is cost-effective for exhibitors, it compromises attendee privacy since the data is exposed to any unauthorized scanner. Our solutions focus on enhancing security and privacy in the lead retrieval process at events.
Methods of Embedding Information in Badges
- Human-Readable ID Only: The simplest method involves embedding just a badge ID that appears meaningless on its own. The corresponding personal data is securely stored on a database, accessible behind a password-protected website only to authorized exhibitors.
- Encrypted ID and Contact Information: A more secure approach involves encrypting both the ID and personal data before embedding it in the badge’s barcode. Our specialized app decrypts this data instantly upon scanning with secure devices, ensuring that only authorized exhibitors have access to sensitive information. This method uses AES 128-bit encryption, rendering the data unreadable by standard consumer QR code readers.
Choosing the Right Method for Your Event
The decision on which method to use depends on the specific needs of the event and the technology provider. For a comprehensive discussion on the best options for your events, feel free to contact support@CodeREADr.com.
Incorporating advanced QR code scanning and barcode scanning technologies in event management not only streamlines the lead retrieval process but also significantly enhances data security. As we move forward, adopting these encrypted solutions will be crucial in complying with privacy laws and safeguarding attendee information.